With ReCyF, for Référentiel Cyber France (Cybersecurity Framework for France), ANSSI (the French national cyber agency) is providing the entities concerned with an operational framework to move forward with their compliance efforts, particularly under NIS 2, while the vote on the transposition law is still pending.
Structured around 20 security objectives, each supported by acceptable means of compliance, ReCyF confirms the need to bring physical security and cybersecurity together in order to demonstrate compliance.
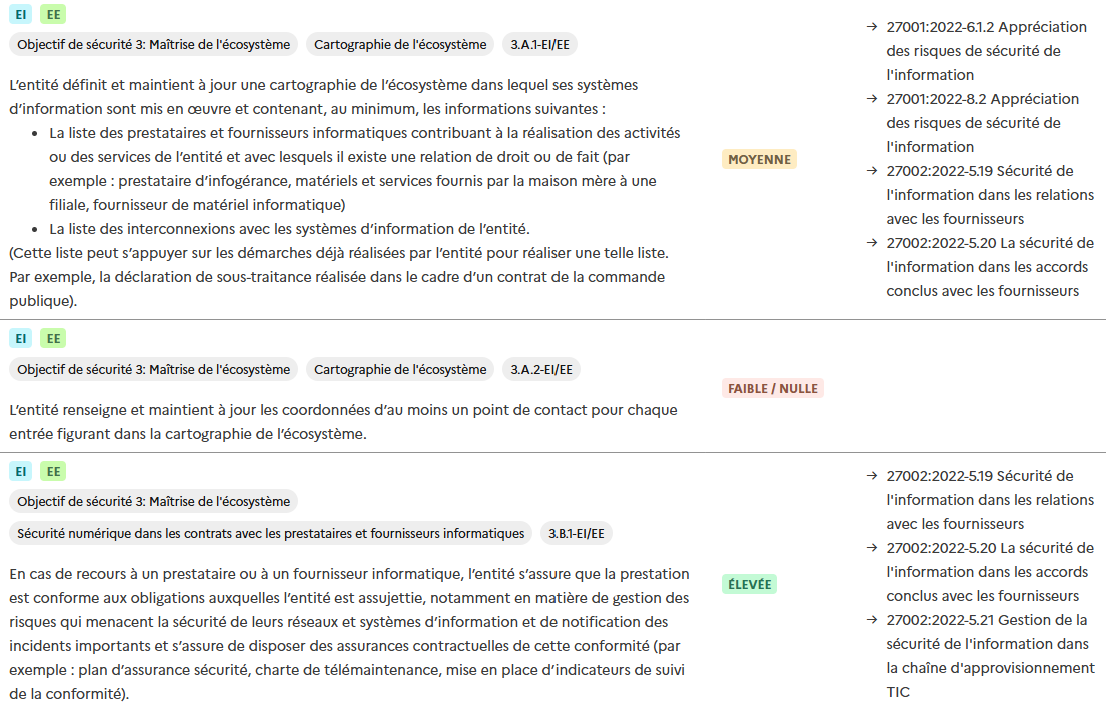
Lastly, ANSSI provides a mapping tool between ReCyF and other international frameworks, including ISO 27001 / 27002 / 27005, in order to carry out gap analyses that clarify and streamline compliance efforts.
1. Introduction to ReCyF
ReCyF is the French cybersecurity framework referred to in the current draft law (Draft law on the resilience of critical infrastructures and the strengthening of cybersecurity, or PJL):
- It sets out mandatory security objectives that answer the question what?
- For each objective, it provides acceptable means of compliance that answer the question how? These measures are not mandatory in principle, but they make it easier for an entity to demonstrate compliance during an inspection. In some specific cases, however, they may become binding.
ReCyF follows a proportionality-based approach, with 20 objectives broken down into sub-objectives:
- Objectives 1 to 15 apply to important entities (IE) and essential entities (EE). Certain sub-objectives apply only to EEs
- Objectives 16 to 20 apply only to essential entities
ReCyF also specifies that entities may rely on ANSSI-qualified services and on certifications compliant with certain European and international standards and frameworks to demonstrate compliance with all or part of the objectives (see section 5, Mapping ReCyF – ISO 27001 / ISO 27002 / ISO 27005).
Lastly, ReCyF includes explanatory annexes on the underlying rationale and associated risks, as well as correspondences with the articles of NIS 2.
Let us quote Vincent Strubel, Director General of ANSSI, who clarified the conditions for using this version 2.5 dated 17/03/2026:
[ReCyF] will remain a working document until NIS2 has been transposed into French law, but it absolutely should not be left unimplemented until then.
Integrating it into your security strategy now means getting ahead of the compliance requirements that will apply in the future, but it also means and above all protecting yourself against a threat that is already, unfortunately, an all too concrete reality for many victims.
2. The 20 ReCyF security objectives
Objectives applicable to important and essential entities
1. Inventory of information systems
2. Implementation of a digital security governance framework
3. Control of the ecosystem
4. Integration of digital security into human resources management
5. Control of information systems 6. Control of physical access to premises
7. Securing the architecture of information systems
8. Securing remote access to information systems
9. Protection of information systems against malicious code
10. Management of user identities and access to information systems
11. Control of information systems administration
12. Identification of and response to security incidents
13. Business continuity and recovery
14. Response to cyber crises
15. Exercises, tests and drills
Objectives applicable only to essential entities
16. Implementation of a risk-based approach
17. Auditing the security of information systems
18. Securing the configuration of information system resources
19. Administration of information systems from dedicated resources
20. Security monitoring of information systems
3. Convergence between physical security and cybersecurity
ReCyF reflects a fundamental shift: physical security is no longer a peripheral issue, but a core component of cyber compliance. Access to premises, visitor and staff management, system segmentation, traceability: ReCyF requires the creation of a robust and coherent link between physical security and cybersecurity. This is reflected in several objectives:
Governance and physical security (objective 2)
“Implementation of an information systems security policy and related policies including, at a minimum, provisions on the use of encryption, physical and logical access control, and review of the application of implemented security measures.”
Physical security is not simply an operational field measure; it must be governed, formalized and managed.
Human resources and physical security (objective 4)
“The entity defines and implements a process for managing arrivals and departures [providing for] the deactivation of all logical access to information systems and physical access to premises and rooms.”
Offboarding must be unified and requires coordination across functions (HR, IT, Security). Ideally, this coordination should rely on appropriate and reliable solutions for managing access rights.
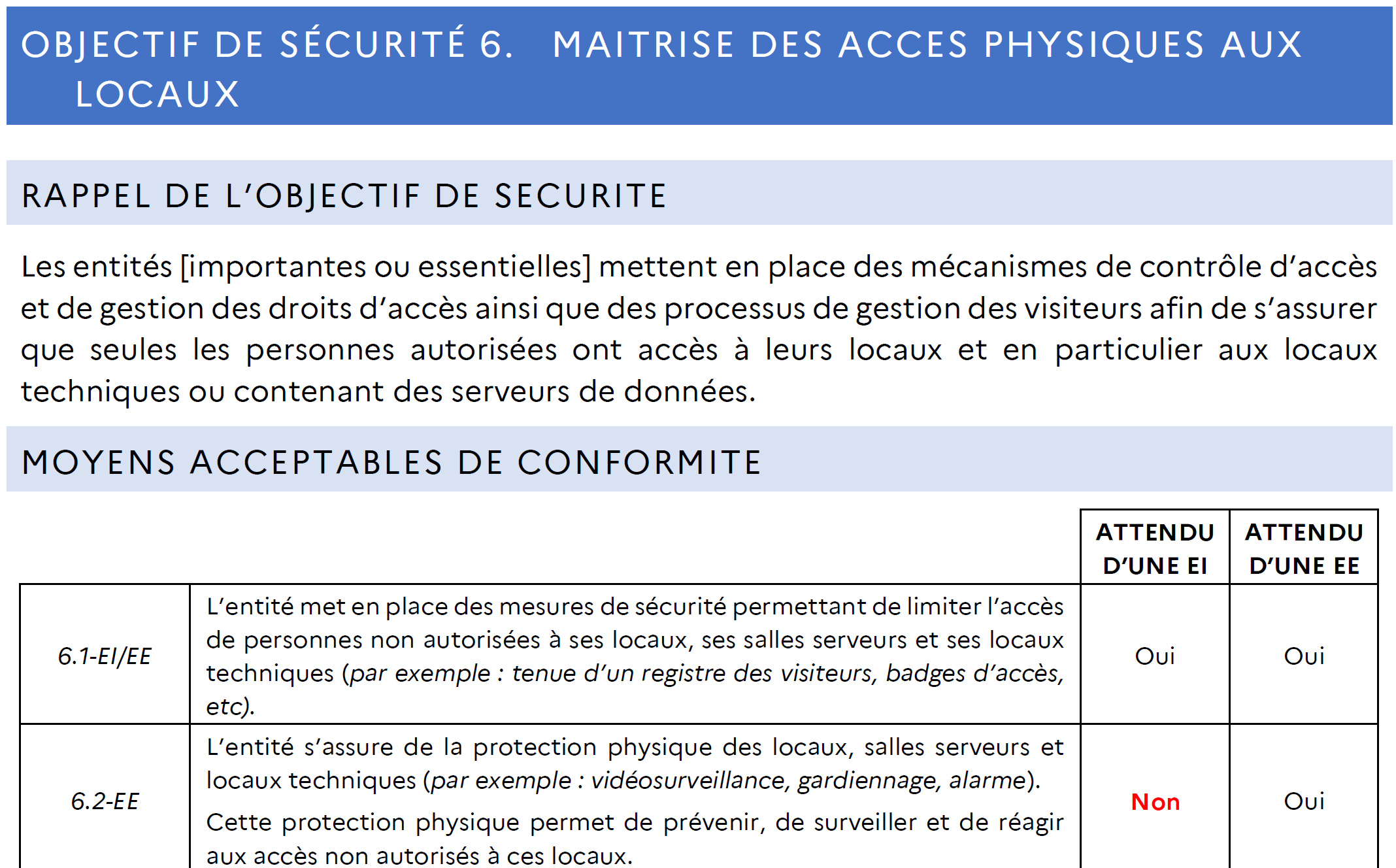
Control of physical access (objective 6)
“[Important or essential] entities implement access control mechanisms, access rights management mechanisms, and visitor management processes to ensure that only authorized persons have access to their premises, and in particular to technical rooms or rooms containing data servers”
This objective is entirely dedicated to physical security. It calls for solutions tailored to operational needs and capable of addressing modern security challenges. The management of external persons, a genuine security challenge, applies to all entities.
- 6.1 IE/EE: limitation of unauthorized access to premises, server rooms and technical rooms, with explicit examples: visitor logs, access badges
- 6.2 EE: physical protection of sensitive premises with examples: video surveillance, security guards, alarms; and this protection must make it possible to prevent, monitor and respond
- 6.3 EE: allocation of physical access rights strictly on a need-to-know / need-to-perform basis
- 6.4 IE/EE: external persons accessing technical rooms and server rooms must be escorted or duly authorized
Physical and/or logical segmentation of information systems (objective 7)
“[Essential] entities segment their information systems into coherent security zones and control communications between these security zones for users, service providers and suppliers.”
Entities identify, with justification, the information systems to which the security objectives will apply. These systems must then be segmented according to their criticality, and the required security level may go as far as physical segmentation to ensure access can be controlled with certainty.
Hybrid threats (objective 9)
“[Important or essential] entities implement mechanisms to protect the resources of their information systems against malicious code”
This objective addresses equipment management, including employees’ personal devices (phones, hard drives, USB keys, etc.). When infected, these personal devices can serve as attack vectors. Once introduced into and connected within the entity, cyber defenses can be bypassed if no strategy / procedure is in place.
4. Choosing your physical security solutions
These objectives must first be considered as a whole, not in isolation. This makes it possible to identify solutions capable of covering several objectives, while keeping operational workload and budget under control.
For example, a suitable conventional access control system (badge, reader, controller, management system) will enable strict access control (meeting objective 6.1 for important entities). In addition, it will:
- Simplify visitor management, including for service providers requiring access to critical areas
- Define security levels suited to each area
- Ensure traceability of individuals through logs
- Facilitate access rights management from employee onboarding to departure
Do not forget that compliance is temporary. Some obligations, currently limited to essential entities, will gradually extend to important entities in response to the evolving threat landscape.
When selecting your security solutions, it is essential to anticipate the raising of security levels.
Our strongest recommendation is to prioritize scalable, customizable and durable solutions, as also recommended by ENISA, which supports:
- open solutions that make support easier through a cross-border support network, from local CSIRTs to European CERTs
- interoperable solutions in order to create coordinated responses in the event of a threat
- standards that harmonize and raise security levels while making required evolutions easier
- certifications that clarify the level of security achieved, in France and across Europe
This position is shared by SPAC Alliance, which promotes the sovereign high-security communication protocol SSCP and actively contributes to legislative and standardization work at both national level (updates to the ANSSI guidance) and European level (standard 16 under the Cyber Resilience Act through the HESTIA project).
5. Mapping ReCyF – ISO 27001 / ISO 27002 / ISO 27005
The MesServiceCyber website operated by ANSSI provides a mapping tool designed to align ReCyF objectives and sub-objectives with several ISO 27k frameworks. As a result, if you hold certifications such as ISO 27001 or ISO 27005, you will be able to identify the level of correspondence with ReCyF objectives and sub-objectives (low/none, medium or high). This tool will therefore enable you to carry out a reliable gap analysis and take the actions needed to complete your compliance journey.